May the (En)Force(ment) be with you.
Posted on: 13 July 2015
By: wolfeg
No Comments »
Filed under: Uncategorized
Or, security lessons from Star Wars.
Star Wars Episode IV: A New Hope, is more than just an epic tale of the galaxy wide struggle between the Rebellion and the Galactic Empire, and the triumph of good over evil. It is also a great example of how a series of basic security flaws can cost the most powerful organisation in the galaxy dearly.
In his position of executive leader of the Empire, Darth Vader certainly didn’t lack resources. With huge teams of highly trained and motivated personnel at his command, plus state of the art technology and hardware, he knew what assets needed protecting. However the measures taken to protect those assets were sorely lacking. Ultimately the Empire was compromised by a fatal combination of weak security policies and poor practice.
Let’s take a look at some of the key security mistakes made by the Empire in Star Wars IV, how those mistakes were exploited and what we can learn from them.
Data Leak Prevention (DLP):
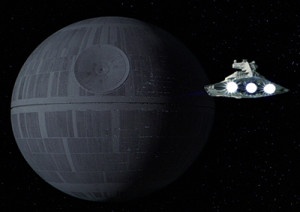
In the (now legendary) opening sequence of the film, Darth Vader and his Storm Troopers board a Rebellion vessel to recover intercepted blueprints of the Empire’s new terror weapon, the Death Star. So far so good. The Empire has detected a potentially dangerous data leak, and has acted swiftly to contain it.
However, the Empire’s good intentions were let down by poor execution. The search of the ship was too focused on finding Princess Leia, enabling the stolen data to be downloaded onto a consumer device (R2D2), which escaped the captured ship in an escape pod. During a period of security lock down, the Imperial forces detected the launch of the pod. They also knew that the pod contained two droids, but they let it go despite the prevalence of droids in the Star Wars universe. They also overlooked the fact the plans are only data and not alive, as at that time – it wasn’t a droid they were looking for!
This lesson teaches us there are multiple vulnerabilities that can result in data loss: USB flash drives, consumer devices, email, instant messaging (IM). In the Star Wars example the data lost was the Death Star schematics, the reality for the University is that data loss could damage the reputation of the University or its’ partners. Another lesson to learn from this example is that if we are suspicious of something that doesn’t seem to be right, then just ignoring it is probably the wrong thing to do.
No technology is infallible:
The stolen blueprints were put to good use by the Rebellion to create a highly targeted attack on the Empire’s primary security device, the Death Star. However, at the Imperial board meeting convened to discuss the ramifications of the data breach, Imperial executives were more concerned with points scoring and squabbling with each other, instead of working together to locate and then close off all possible vulnerabilities.
Darth Vader warned Admiral Motti not to be too proud of the technology the Death Star represented. Motti retorted that Vader’s knowledge and use of the Force had not revealed the location of the stolen data. Vader found Motti’s lack of faith disturbing, but he should have been more concerned that the meeting had failed to find a way to resolve the problem and fix the vulnerability. A simple precaution such as shielding the exhaust port, or welding a couple of metal bars over it could have been enough to secure this flaw in the design.
Neither had grasped the fact that it doesn’t matter how strong you believe your security infrastructure to be there is always the possibility of vulnerabilities being introduced through simple human errors or poor planning and design. Keeping networks and data secure requires clear policies, with people following them. It also needs a coordinated effort across the IT and security teams. Having security products alone is not sufficient to protect networks and data.
Authentication and Access controls:
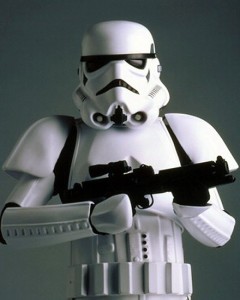
When the Millennium Falcon is captured in a tractor beam and brought into the Death Star, the Empire fails to properly inspect the vessel for payloads that could present a risk. Then the rebel crew exploit the Empire’s weak visual authentication tests by stealing Storm Trooper uniforms. This gives them unchallenged access to the Death Stars’ interior, networks and defence systems.
This highlights two common security issues we can be more aware of. First, without strong user authentication it’s easy for a potential attacker to appear familiar and trustworthy. Simple visual checks carried out by the Empire such as: is the person wearing an Imperial Storm Trooper uniform? Check. Do you nod when asked if you are TK421? Check. Access granted! Clearly these were not enough. When securing physical access to a location by requiring photo ID, or securing electronic access by requiring a user name and password – we can see that authentication of identity is vital.
Secondly, it is not appropriate to give all members of staff, contractors and third parties full access to all parts of our network, resources and data; as the Empire appears to do for Luke and his friends. We should ensure that only those authorised to access and use specific data can do so.
Consumerisation or Bring Your Own Device/Droid (BYOD):
Having bypassed the Empire’s weak authentication systems on board the Death Star, R2D2 is able to access highly confidential data on the Death Star itself (how and where to disable the tractor beam and the location of Princess Leia), simply by plugging in to an easily accessed wall port. The port looks so much like a power outlet, even R2D2 accidentally plugs in to one by mistake in a later film!
R2D2 is also able to control various parts of the Death Star’s physical environment from this access point such as lifts, garbage compactors etc. What’s more, R2D2 isn’t just a portable storage device. It is a self-propelled and intelligent robot that could not only take the data anywhere, it can also use that data selectively itself. This creates a real BYOD (bring your own device/droid) problem for the Empire.
Ultimately, the Empire had clear strategic goals, enormous technology and manpower resources in place, yet it failed to apply proper security policies to manage these resources effectively. If it had, it could have made things much harder for the Rebels and crushed the Rebellion swiftly. However, if the Empire had been successful in preventing data loss by tackling it’s vulnerabilities, there probably wouldn’t been any more sequels to the film, which consequently would have ended within the first 10 minutes or so!
Graeme Wolfe
14/07/15
With thanks to Terry Greer-King from CheckPoint technology, for the original article.